Mojave Security
Most apps from this site are 1) saved as read-only to inhibit malicious code injection, 2) codesigned with my authorized developer ID so that they will break if they are so edited and 3) packaged in a disk image that is also codesigned with my developer ID so that the disk image will not open if its contents doesn't check out. You—the user—also have Gatekeeper security options to allow just Mac App Store and/or developer signed apps.
Additionally, I would hope that my own personal reputation as a "good dude", cultivated over almost twenty years as an AppleScript developer, would also attest to the safety of my scripts. But that won't be the case for bad actors attempting to hijack processes on your Mac.
Apple is introducing a new level of security in Mojave called "AppleEvent Sandboxing". It effects how AppleScript is or isn't permitted to access certain locations and processes on your Mac.
When you launch an AppleScript of mine for the first time on macOS 10.14 Mojave you'll see something like this:
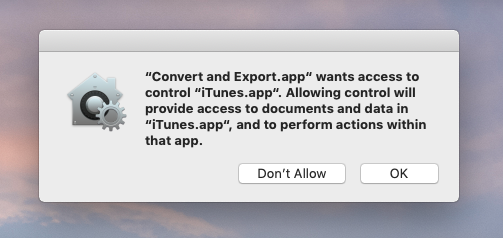
This message will appear before the app or script starts runniing or it may appear a little later into the launch, if and when it actually attempts to access iTunes. AppleScripts that work with multiple apps will display an alert for each of those apps.
(Personally, I think that "OK" button should say "Allow", but, whatevs.)
This is a new layer of protection that attempts to prevent AppleScripts, and other apps that use AppleScript, from controling apps and accessing data without you knowing about it. When you click "OK", you've acknowledged to the system that you indeed intend to use the script with said application. Once so acknowledged, you shouldn't see the dialog(s) again for that particular script.
Users of scripts that have targeted "System Events" may be familiar with this process when Accessibility requires a similar acknowledgement. This is a little different since it falls under the purview of Security & Privacy. In fact, if you go to System Preferences > Security & Privacy > Privacy > Automation, you will see the list of apps that use automation and which apps they target:
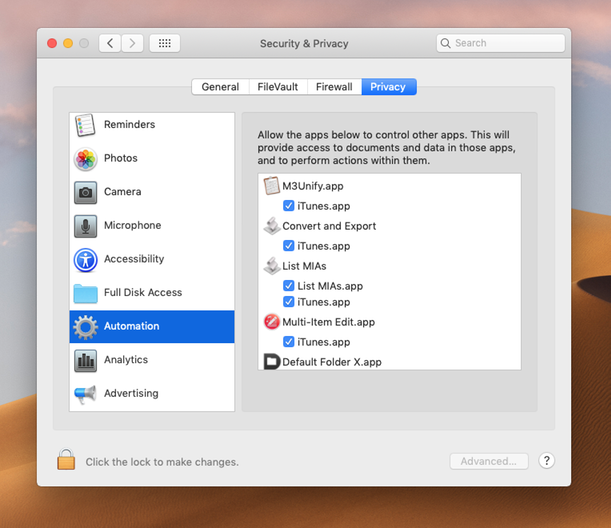
The list of apps on my machine is way longer than appear here.
If necessary, you can uncheck an app if you suspect the listed AppleScript is up to some funny business. Or, if you clicked on "Don't Allow" when first asked, you can enable access for a particular app.
Felix Schwartz has posted some first looks at AppleEvent Sandboxing and it's worth a read until Mojave is officially released and Apple tells us more.
